CrateCTF-2024
Langtidsminne
A user has fallen victim to a phishing attack, unknowingly downloading and executing an unverified program. According to the challenge description the program was executed around 14:12. We are given a memory dump from the event and our task is to identify the malicious program that was executed.
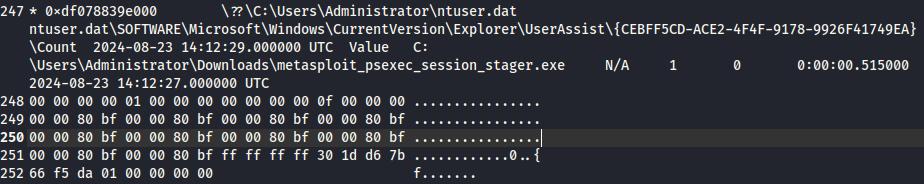
To analyze the memory dump we can use the program Volatility. After trying a few different plugins/commands from a Volatility cheat sheet (https://book.hacktricks.xyz/generic-methodologies-and-resources/basic-forensic-methodology/memory-dump-analysis/volatility-cheatsheet) we found one that shows what programs was run by the user, so called UserAssist keys.
python3 vol.py -f memdump.elf windows.registry.userassist.UserAssist > userassist
We preform the UserAssist analysis and save the output to a file. Looking through the file we find that around 14:12 a suspicious program called metasploit_psexec_session_stager.exe was exectued.
Wrap the program name inside the cratectf tag and we got the flag: cratectf{metasploit_psexec_session_stager.exe}
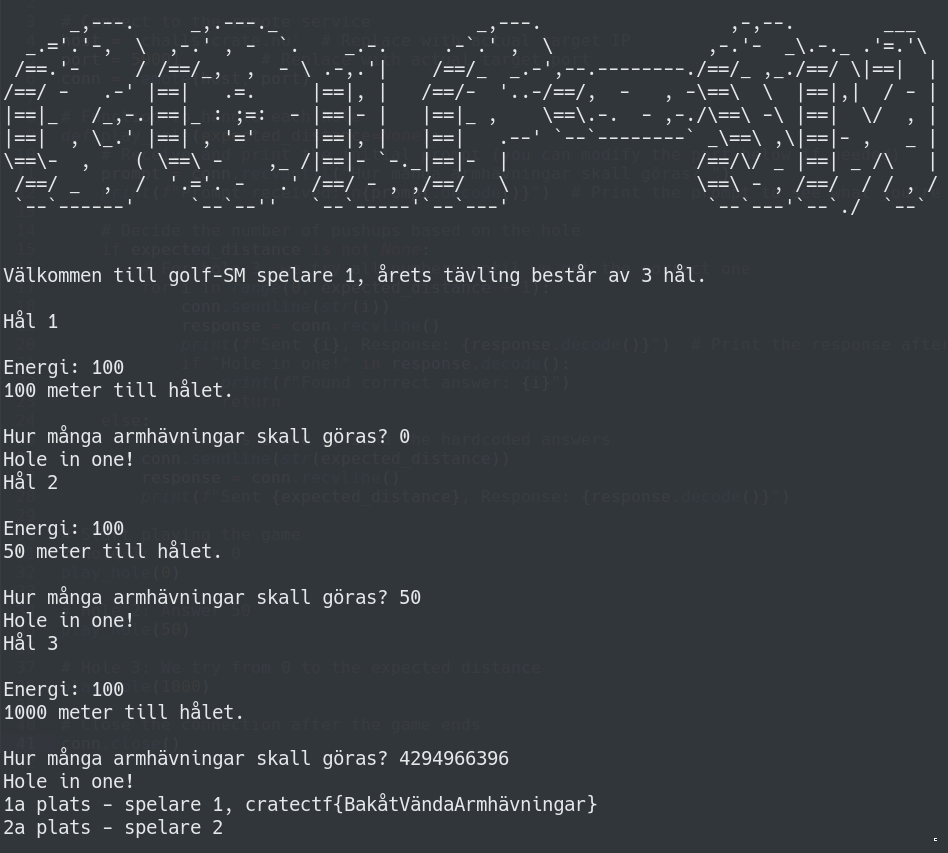
Golf-SM
In this challenge we play golf over netcat. After some elaboration and testing we realize that we want to input -900 to score a hole in one on the last hole. However, negative numbers are not allowed. We can bypass this by using an integer overflow technique. A 32 bit integer can hold numbers up to 232 - 1 (4294967295). In the program the number 4294967296 is interpreted as 0. So if we input 232 - 900 = 4294966396 we score a hole in one and get the flag.
cratectf{BakåtVändaArmhävningar}
Red teaming?
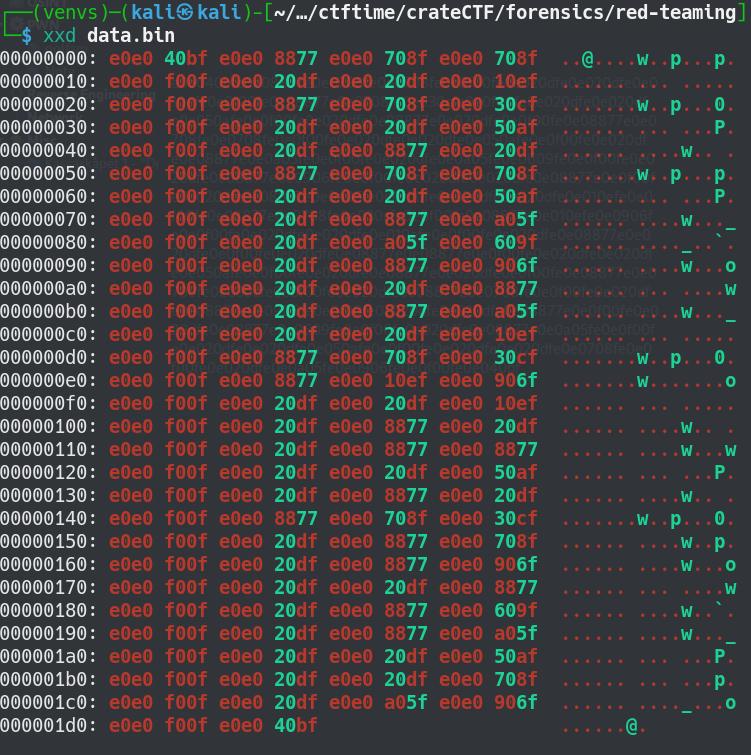
The challenge description tells us something about a guy watching TV and we are given a file with binary data.
We inspect the data with xxd
xxd data.bin
Googling the hex values e0e040bf we came across a website with remote control binary codes (https://tasmota.github.io/docs/Codes-for-IR-Remotes/). These match our data perfectly.
By using the table from the website and python we were able to translate the instructions in our binary data and get a list that looks like this.
xE0E040BF - TOGGLE ON/OFF The numbers in between the strings TOGGLE ON/OFF and MUTE seems to be ASCII numbers.
0xE0E08877 - 0
0xE0E0708F - 9
0xE0E0708F - 9
0xE0E0F00F - MUTE
0xE0E020DF - 1
0xE0E020DF - 1
0xE0E010EF - 4
.
.
.
0xE0E020DF - 1
0xE0E0A05F - 2
0xE0E0906F - 5
0xE0E0F00F - MUTE
0xE0E040BF - TOGGLE ON/OFF
Using python we can extract these numbers and translate them into readable text and we get the flag.
cratectf{infra-redteamingftw}